Publications
- Liu, W., Wang, W., Chen, H., Wang, X., Lu, Y., Chen, K., Wang, X., Shen, Q., Chen, Y. and Tang, H., 2021, June. Practical and efficient in-enclave verification of privacy compliance. In 2021 51st Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN) (pp. 413-425). IEEE.
- Chen, H., Chen, H.H., Sun, M., Li, K., Chen, Z. and Wang, X., 2023. A Verified Confidential Computing as a Service Framework for Privacy Preservation. In 32nd USENIX Security Symposium (USENIX Security 23) (pp. 4733-4750).
- Reed, A.C. and Reiter, M.K., 2023, July. Optimally Hiding Object Sizes with Constrained Padding. In 2023 IEEE 36th Computer Security Foundations Symposium (CSF) (pp. 505-520). IEEE.
- Wang, Z., Guan, J., Wang, X., Wang, W., Xing, L., and Alharbi, F., 2023. The Danger of Minimum Exposures: Understanding Cross-App Information Leaks on iOS through Multi-Side-Channel Learning. In Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security (CCS 2023) (pp. 281-295).
- Zhao, S., Xu, P., Chen, G., Zhang, M., Zhang, Y. and Lin, Z., 2023. Reusable Enclaves for Confidential Serverless Computing. In 32nd USENIX Security Symposium (USENIX Security 23) (pp. 4015-4032).
- Zhou, L., Liu, Z., Zhang, F., and Reiter, M. CrudiTEE: A Stick-and-Carrot Approach to Building Trustworthy Signing Key Management with TEEs. In 6th Conference on Advances in Financial Technologies.
- Zhou, Q., Dang, S., and Zhang, D. Ctchecker: a Precise, Sound and Efficient Static Analysis for Constant-Time Programming. In Proc. of the European Conference on Object-Oriented Programming, 2024.
- Chen, H.H., Chen, H., Sun, M., Wang, C., and Wang, X., 2025. Picachv: Formally Verified Data Use Policy Enforcement for Secure Data Analytics. In 34th USENIX Security Symposium (USENIX Security 25).
- Chen, H., Zhou, Q., Yang, S., Han, X., Zhang, ., Zhang, D., and Wang, X., (2025). Agora: Trust Less and Open More in Verification for Confidential Computing. In Proc. of Object-Oriented Programming, Systems, Languages & Applications Conference (OOPSLA), 2025.
- Rosenberg, M., Shih, M., Zhao, Z., Wang, R., Miers, I., and Zhang, F. (2025). ZIPNet: Low-bandwidth anonymous broadcast from (dis)Trusted Execution Environments. Proceedings on Privacy Enhancing Technologies.
- Liu, W., Chen, H., Huai S., Xu, Z., Wang, W., Wang, X., Zhang, D., Li, Z., Tang, H., and Liu, Z. (2026). Characterizing trust boundary vulnerabilities in tee container systems: An empirical study. To appear in the ACM International Conference on the Foundations of Software Engineering (FSE), 2026.
- Jiang, Q., and Zhang, D. (2026). VeCT: Secure and Efficient Constant-Time Code Rewriting with Vector Extension. To appear in 35th USENIX Security Symposium (USENIX Security), 2026.
- Wang, W., Shi, F., Vilardell, D., and Zhang, F. (2026). Cirrus: Performant and Accountable Distributed SNARK. in NDSS Symposium 2026, 2026.
Ongoing works: - Zhao, S., Wang, W., Li, N., Lin, Z., 2025. STYX: Collaborative and Private Data Processing Using TEE-Enforced Sticky Policy. In submission.
- Huang, W., Wang, C., Wang, X., 2026. Towards Practical Oblivious Databases with Heterogeneous TEEs and GPU Acceleration. In submission.
Artifacts
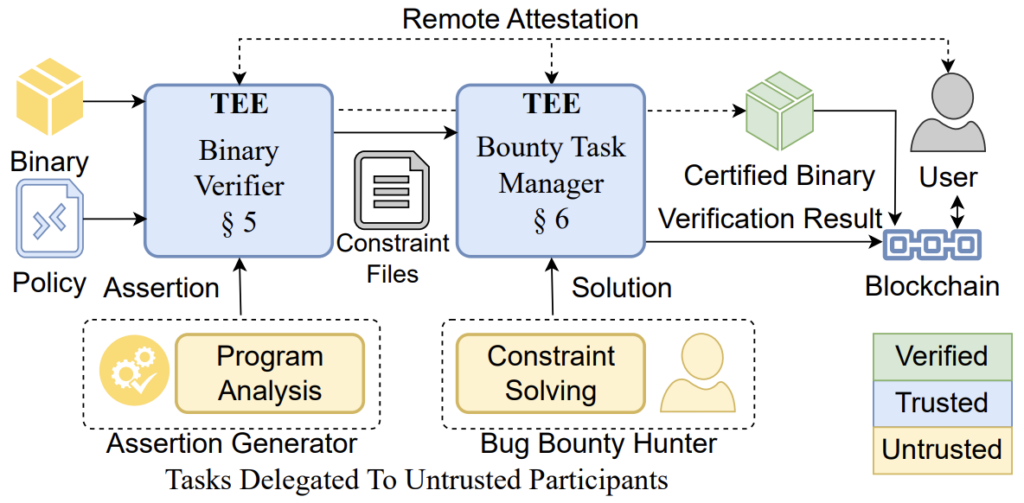
Agora
Agora is a binary verification framework for confidential computing that makes verification more open, auditable, and trust-minimized. By combining validator-centric design with blockchain-based task management, it supports practical verification of security policies such as software fault isolation and side-channel mitigation.
Deflection
Deflection is an SGX shielding runtime (SGX middleware) that can run nearly unmodified C/C++ code securely. Other than Graphene-SGX, SCONE, Occlum, etc., it can protect the code secrecy and data confidentiality at the same time.

PoBF
Proof of Being Forgotten (PoBF) and PoBF-Compliant Framework (PoCF) prototypes.

Reusable Enclaves
This is a research project aims to solve the cold start problem without sacrificing the security by creating a method to securely reuse the enclave. The paper is accepted to 2023 USENIX Security Symposium.

Picachv
We advance the research in this area by introducing Picachv, a lightweight runtime security monitor that can be seamlessly integrated into existing query execution engines, plus verifiable formal guarantees written in Coq.
Hosted or Sponsored Workshops
- Workshop on Artificial Intelligence System with Confidential Computing (AISCC 2024) Co-located with NDSS Symposium 2024, San Diego, CA
- iDASH Privacy & Security Workshop 2025, Atlanta, GA
